Photonics enables quantum key distribution to secure the world’s data.
NINO WALENTA AND LEE OESTERLING, BATTELLE
Quantum technology is no longer science fiction. Election results, health data, mobile phone communications, sensitive business information, banking transactions and user IDs — more and more applications are secured with quantum key distribution (QKD) in quantum telecommunication networks. The longest-running quantum network has been in operation for more than seven years, while the largest quantum network features more than 50 nodes. Today, quantum links have been established with satellites, planes and balloons.

Illustration of the Chinese nationwide quantum key distribution (QKD) network, which includes a planned satellite QKD link. Courtesy of Qiang Zhang, USTC.
Underlying the expansion of quantum networks is photonics technology. To comply with the compactness, robustness, reliability and costs of modern telecom infrastructures, implemented systems rely on well-established standard components such as electro-optical modulators, semiconductor detectors and integrated photonics circuits. At the same time, they push their limits toward maximum modulation ratio, low-noise single-photon sensitivity and ultra-low coupling and propagation losses, respectively.
As data transfers skyrocket in both size and frequency, more and more countries and companies are investing in large-scale quantum communication networks. To date, about 2.9 exabytes of data—16 million Blu-ray discs—are transmitted through the Internet every day. The security of this data relies heavily on cryptographic keys that must be securely distributed and shared between parties. Once these keys are established, they are used to encrypt transmitted data to protect secrecy, or for authentication to prevent forging against eavesdroppers. However, protecting data becomes more and more vulnerable as the security of the mathematical algorithms that are used to distribute the keys is increasingly threatened by improving computer power, new attack algorithms and, in particular, the emergence of quantum computers.
Using special quantum algorithms, a quantum computer is able to perform integer factorization and brute-force searching much faster than conventional computers. Consequently, widely used cryptosystems that base their security on the premise that certain computational problems are difficult to solve are threatened. Currently, multiple technological approaches toward scalable quantum computers are being developed, including quantum processors based on integrated photonic chips. Some experts expect that in 10 to 15 years quantum computers will be powerful enough to break the key distribution schemes that are currently used. Hence, already today data that is supposed to remain secure for more than 10 to 15 years has to be considered vulnerable since an eavesdropper can simply record the transmitted data and decipher it once a quantum computer is available.
Encoding keys in photons
While quantum physics poses a major threat to the security of our data, it luckily offers an elegant solution to the security
problem: quantum key distribution. Instead of using mathematically difficult problems, QKD protects the distribution of cryptographic keys by encoding information in quantum states of —for example — the polarization, phase or quadratures of photons. Using quantum states allows security to be based on fundamental physical and quantum-information theoretical principles, expressed by the no-cloning theorem, which states that it is physically impossible to produce perfect copies of unknown quantum states; the Heisenberg uncertainty principle, which puts forth that measuring unknown quantum states inevitably introduces detectable errors; or properties of quantum entanglement, which set a fundamental limit on the information leaked to unauthorized third parties. Because of these principles, any eavesdropping attempt inevitably introduces detectable errors. The number of errors directly quantifies how much information about the key could have been gained, even with the most powerful future strategy and hardware, including quantum computers. After the quantum exchange, a number of post-processing steps, known as key distillation, correct the introduced errors and amplify the security of the key by removing any leaked information. In short, QKD allows precise quantification of security of the keys before they are used, and there would be no way for an eavesdropper to wait for future progress in technology to obtain secrets. By continuously providing such highly secure keys, QKD is especially beneficial for symmetric cryptographic algorithms like AES (Advanced Encryption Standard).

The plane with QKD hardware in an optical communication terminal (inset) that created the first QKD link with a ground station (right). Courtesy of University of Munich.
Most QKD systems are built around standard telecom components like modulators, semiconductor and superconductor detectors, and photonic lightwave circuits, but push their limits to meet the high requirements of QKD. This includes maximizing the extinction ratio of modulators and the signal-to-noise ratio of single-photon detectors, and minimizing the coupling and propagation losses in photonic circuits and other optical components. Eventually, these improvements might bring benefits to standard telecom systems, too.
Protecting financial transactions, election results
For more than a decade, QKD has been used in commercial applications. In 2004, QKD helped to protect a financial transaction between the Vienna City Hall and the headquarters of Bank Austria Creditanstalt. Since 2007, commercial QKD systems have been used regularly by the government of Geneva, Switzerland, to protect the transmission of election results against corruption during transmission. Since then, several businesses have used QKD to protect their data links to backup sites and disaster recovery centers.
Since QKD is a point-to-point technology and its maximum transmission distance is ultimately limited by fiber losses to a few hundred kilometers, these applications are well-suited. In order to overcome these limits and extend QKD to larger networks with many users and over greater distances, experts have proposed connecting multiple QKD links in a nodal network of trusted relays. Within these networks, keys are established between any two nodes protected by QKD, but intermediate nodes must be protected against tampering.
On the road toward today’s large-scale QKD networks, several field tests demonstrated their compatibility with photonic telecom networks and the interoperability of different QKD systems in a common network. They protected several applications, including phone and video teleconferences, the distribution of data collected at the CERN laboratory, and the remote security surveillance of a soccer stadium during the FIFA World Cup 2010. Along with continuous improvements in performance and costs of optical components that facilitated better reliability, integration, mass production and ease of use, today’s QKD network systems reliably protect sensitive information of numerous adopters every day.

Projected QKD network rollout in South Korea. Courtesy of Nicolas Gisin.
To find today’s most ambitious QKD networks, one must look to the Asian “Quantum Triangle” between Japan, South Korea and China. In 2016, the first stage of a South Korean nationwide QKD network began operation between Seoul, Bundang and Suwon. Over the next five years, the consortium led by SK Telecom envisions its expansion to a national administrative QKD network with several thousand nodes for public administration, police and postal services.
Tokyo’s impressive quantum network began operating in 2010 and connects four QKD hubs across the city with systems developed by NEC, Toshiba, NTT and others. The QKD keys are supplied to government agencies, network operators, NICT research facilities and Tokyo University. These keys protect sensitive data and teleconferences. Recently, a link that transfers genome data between an analysis center and genome database center was included. Its QKD ensures that the genomic data remain secret.
In 2015, the Tokyo network demonstrated smartphone applications made by NEC and Mitsubishi that were topped up with highly secure keys from QKD to use for end-to-end encryption of phone calls. Demonstrations also showed how a hospital visit might look in the future, in which patients use their QKD-enhanced smartphones to authenticate and protect the transfer of their personal medical records using quantum keys.
The largest — and ever-growing — quantum network to date was deployed between/in metropolitan areas in China. It started in 2007 with a QKD network in Beijing’s commercial telecomm infrastructure and, since 2010, a much larger quantum network has operated in Hefei. This network of over 45 nodes connects city government agencies, military units, financial institutions and health-care offices.
Another large QKD network consisting of 50 nodes began operating in Jinan in 2014. This network provides QKD keys to 90 users at 28 institutions and commercial customers, including the China Industrial and Commercial Bank, Xinhua News Agency, the China Banking Regulatory Commission and various government offices. Within the next few months, China plans to complete the world’s longest quantum communication link, a 2000-km QKD backbone between Shanghai, Hefei, Jinan and Beijing. Evolving technology — more compact, robust and reliable components — is helping make these longer networks possible.
Intercontinental QKD network
The next frontier for QKD technology is space. China’s aerospace engineers are developing QKD links using satellites that serve as mobile nodes that would extend a network to remote locations or even globally. By 2020, China envisions an intercontinental network between Asia and Europe.
Although these ideas may sound far-fetched, recent advances are raising hopes. In 2007, a team of European researchers realized a 144-km QKD link between two ground observatories on the Canary Islands of La Palma and Tenerife. The link saw atmospheric losses and turbulence equivalent to low-orbit satellite links. In 2010, a QKD link to a hot-air balloon floating at an altitude of 20 km was successfully achieved, simulating the vibration, motion and velocity of low-orbit satellites. In 2013, scientists created a fully functional QKD link between a ground station and an airplane moving at 290 km/h at a distance of 20 km at the same radial velocity as a satellite. And more recently, a research team at the Italian Space Agency and the University of Padova used satellites equipped with a corner cube retroreflector to transmit QKD signals from a transmitter in low and medium orbits over 7,000 km to a ground receiver. These results indicate that taking QKD into space is more than just a promising idea.
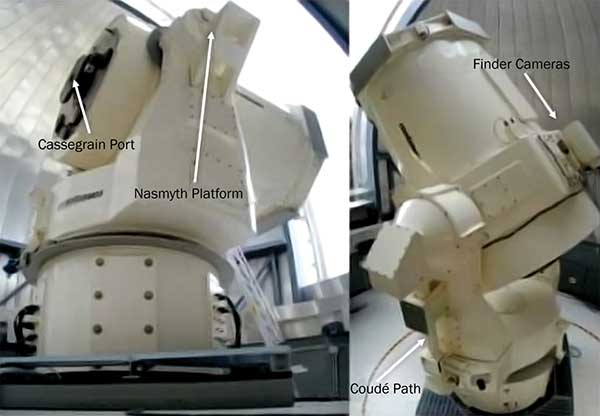
The telescopes at the Matera Laser Ranging Observatory in Mater, Italy, that demonstrated the feasibility of QKD from a satellite equipped with a corner cube retroreflector. Courtesy of P. Villoresi (Univ. of Padova) and G. Bianco (Italian Space Agency).
While the examples above focus on long-range QKD network systems, researchers are also looking to put QKD into highly integrated low-cost handheld devices. Eventually, these miniaturized portable QKD devices could be topped-up with keys from quantum terminals and carried in the pocket to protect day-to-day routine and business. Researchers have even proposed putting such miniaturized systems on drones. These devices might establish links with ground stations to protect control communications against spoofing or between drones to transport keys to access remote locations.
As QKD systems advance, the need has arisen for a set of recommended standards and practices. While specific QKD standards are still under development by entities such as the ETSI QKD Industry Specification Group and the Cloud Security Alliance, a recent project by Battelle strives to be the first commercial QKD system that complies with the government’s FIPS 140-2 information security standard. This could help drive the deployment of QKD in environments that strictly require certified devices. Battelle plans to add these systems to its QKD network in Columbus, Ohio, the first commercially funded QKD network in the United States. This network has operated since 2013 and will eventually connect Battelle facilities throughout the country.
Meanwhile, the UK National Quantum
Technologies Programme plans to foster the development of specific QKD standards and to apply them to a QKD network that will enable secure transactions across government agencies, industrial and commercial companies, and the wider public.
Quantum repeater networks
Today’s networks are based on the trusted node architecture and require a certain level of trust in the intermediate nodes. Ultimately, the goal is to replace this architecture with quantum repeater networks that would enable quantum states to be distributed over long distances. This would avoid the need for anti-tamper technology at intermediate nodes.
The obstacle with quantum repeaters is that, until recently, all proposed architecture relied on two critical technologies: efficient sources of entangled photons and cryogenically cooled quantum memories that are able to store the quantum states for a sufficiently long period of time.
Although efficient entangled photon sources are commercially available and significant progress has been made toward quantum memories that support high data rates in multiplexed networks, quantum repeaters are still several years away. Recently, however, new quantum repeater architectures have been proposed that, although relying heavily on entanglement, completely avoid the need for quantum memories. This approach may well accelerate the emergence of quantum repeater networks.
In a world of growing cyber threats, QKD applications promise a new era of secure data transmissions. The technology has been proven; it’s now a question of scale.
Perhaps in the not-too-distant future an everyday user will visit a quantum terminal as casually as an ATM today. The user might load quantum keys onto a pocket-size smart quantum device. As he or she accesses financial and medical data — and as that information traverses the globe — the user would know it is truly secure, confident that even a quantum computer could do no harm.
Meet the authors
Nino Walenta, Ph.D., a principal research scientist at Battelle, recently joined the company to work on an internally funded quantum key distribution network project. He has 10 years’ experience in academic research and development of quantum technologies; email: [email protected]. Lee Oesterling, Ph.D., is a senior research scientist at Battelle and has over 15 years’ experience with the design, fabrication and test of photonics systems and components. He is responsible for the test and development of novel photonics technologies to support quantum information processing applications; email: [email protected].