MARTINA MÜLLER AND MAREK KREHEL, 3D AG
As anti-counterfeiting features,
holograms are present on various products, from banknotes and credit cards to children’s strollers. Most people encounter them every day, yet they are often unaware of their presence. Holograms are subject to continuous research and development and are more recently known in the form of projections. They are even considered futuristic art by some.
The invention of holography tells a long story of research that is based on fundamental laws of physics and optics. Like photography, holography is a way of recording, yet the technologies have substantial differences when it comes to the information captured. As the meaning of the Greek words “holo” (whole) and “gram” (message) connote, a hologram captures the entirety of a scene, with all its visual properties, including the realism of three dimensions1.
Technology and history
Holographic security elements consist of nanostructures that refract light in a very specific manner. They enable 3D effects to be seen on what appears to be
a flat surface. These structures can be originated by means of classical (analog)
holography, where — comparable to classical photography — a photosensitive material is used for recording light. Similarly, a hologram is created by recording
the interference patterns created by lightwaves. To form such patterns, two wavefronts must interfere, which is only possible if the wavefronts are coherent. To guarantee coherence for a specific length, the beam of a single laser is split into two coherent beams. To record a hologram, a system with various optical elements must be set up in a carefully measured manner under specific laboratory conditions: particle-free with high stability (no vibration) and consistent air temperature2.
The roots of holography can be traced back to 1920’s research in x-ray crystallography. The idea for holographic imaging was invented by Denis Gabor in 1947 while he was trying to obtain increased resolution in electron microscopy. His work proved the concept’s validity. Optical holography was not yet successful, however, due to poor quality. The reconstructed image was superimposed on a background, caused by a conjugate image and direct beam. The breakthrough that solved this twin-image problem was an off-axis reference beam technique invented in 1962 by Emmett N. Leith and Juris Upatnieks. Then, with the invention of the laser in the early 1960s, holography had its breakthrough and the technology opened to wide research, resulting in the creation of new techniques of design and types of holograms3.
For several decades, analog optical procedures were the only methods available for creating nanostructures with holographic effects. Advancements in digital technologies in the late 1980s enabled the origination of computer-generated holograms, for which the first patent was filed in 1988. This breakthrough led to the development and invention of various proprietary and commercially available systems. Following the trend of multiple applications of holographic structures, some companies chose to develop their own methods and keep their systems in-house. Others started businesses and sold their systems, such as the KineMax, or variations of the relatively simple and inexpensive dot matrix system. Later, electron-beam (e-beam) lithography was also used because of its ability to form two-dimensional patterns on the nano-meter scale.
In comparison to the expensive, sophisticated, and difficult-to-operate e-beam systems, which were traditionally used by large research centers and universities,
the inexpensive dot matrix systems required minimal training to use. The increase of dot matrix technology enabled a wider range of companies to originate holograms and therefore to replace expert holographers. At least 100 dot matrix systems are now used worldwide, which has resulted in greater accessibility but has also increased imitations and the number of counterfeiters abusing security features. Additionally, while holograms were establishing for security uses, they also became decorative features for promotional and packaging applications, allowing use to spread even more widely.
At the beginning of the century, the rapid development of digital technology had increased the availability of holograms but decreased general trust in them4. Over the past decade, a time of globalization and spread of online channels, the need for security features for anti-counterfeiting has exponentially
risen. Packaging and products are equipped with anti-counterfeiting features that are both overt (effects visible to the human eye) and covert (elements such as nanotext and hidden features visible only with tools) for consumer authentication, as well as for controlling the distribution
chain. Because of the current high demand for solutions, other technologies have developed, especially smart and digital features, such as unique QR (quick response) codes and RFID/NFC (radio frequency identification and near-field communication)5.
Today, the earlier negative associations
with holograms seem to have faded. Holograms remain one of the few valid solutions for true authentication that can implement both overt and covert features, serialization, and smart solutions used for consumer engagement and tracking. With their presence on banknotes, holograms still convey a sense of protection and security in comparison to unknown and newly developed digital solutions. Additionally, holography companies use their specific technology to regularly develop new features such as machine readablity, covert hidden features, or visual enhancements (Figure 1).
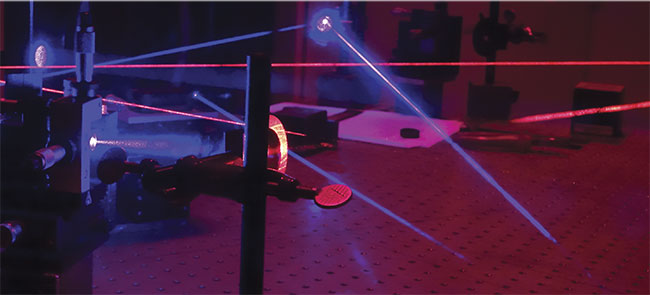
Figure 1. A laser setup on an optical table for classical (analog) hologram origination. Courtesy of 3D AG.
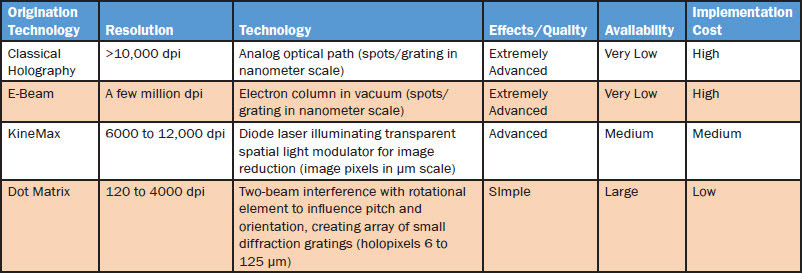
When it comes to the benefits and limitations of the technologies, results show analog holography and e-beam lithography to be more suitable for security applications due to their higher implementation cost and lower availability (Table 1). For every anti-counterfeiting solution with a specifically implemented technology, however, the cost of education is high because the implemented solution needs to be communicated to the general public and to the distribution chain. Both analog holography and e-beam systems are able to facilitate this education and level of security better because they come without pixels, with a high resolution, and with some effects untouched by the digital holography technologies.
Table 1.
A summary and comparison of the main types of holographic nanostructure origination techniques
Materials and methods
One of the main goals of a recent
study6 was to compare types of holographic techniques used for anti-
counterfeiting methods. A relatively complex hologram was originated that consisted of a true-color hologram, a real 3D model, 2D/3D depths, sinusoidal grating dynamic effects, and matte white structures. Accurate combinations of these structural effects in a complex design were chosen for the study, to deliver a strong fundament for a comparison of technologies. Multiple companies that originated holographics were contacted and asked to generate similar-looking holograms, either by receiving the graphic production data or without any graphic data, to represent a counterfeit. Four were created (Figure 2).
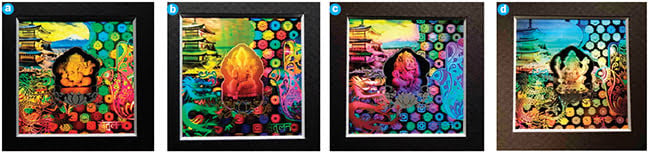
Figure 2. Photographs of the four nickel molds with holographic structures. Multiple light sources were used for clarity of effects. Analogue origination (a), e-beam origination (b), dot matrix origination (c), and counterfeit (d). Courtesy of 3D AG.
These four holograms manufactured by four parties set the basis for the empirical evaluation. The described holograms were presented together with a questionnaire to about 100 randomly chosen customers who were asked to observe them.
Results and discussion
Based on the results of the questionnaire, three main questions were evaluated and hypotheses offered.
Are holograms generally trusted?
Customers surveyed were generally
not influenced by fear of counterfeits, because 53% of those surveyed had never
searched for a security feature on a product. When asked what features they knew of, 25% didn’t know a single anti-counterfeiting approach. From the 75% that could name an approach, 51% named only one, 35% named two, and only 14% named more than three. Among the
19 approaches named, holograms were
the most well known (mentioned by 37 of
the total surveyed), followed by visual and haptic control (16), watermark (15),
serial number (11), chip (7), tamper-evident seal (6), and label and source of origin (4). Given the fact that 25% of all surveyed didn’t know how holograms
are made, there seems to be a mysteriousness about holograms. When questioning the associations people made with holograms, 55% conveyed security, 36%
said quality, and 29% mentioned consumer protection; 18% had no association, 4% expressed uncertainty, and 10% thought about compliance. Even though only 55% of the surveyed had never suspected a hologram could be fake — according to a statistical distribution of points to the dimensions of trust and
distrust — the results convey that holograms are generally trusted for security.
Can an uneducated consumer identify the relevant characteristics and effects to detect a counterfeit hologram?
When comparing the classical hologram to the counterfeit dot matrix version, 97% of those surveyed detected the dot matrix as the counterfeit (Figure 3). The manufacturer clearly did not have the original files for production, and the reproduction was visible by its low resolution and the quality of the pixels and imagery. Although most consumers do not have the ability to compare holograms at point of sale, it is believed that an uneducated consumer could identify sufficient characteristics to detect a counterfeit.
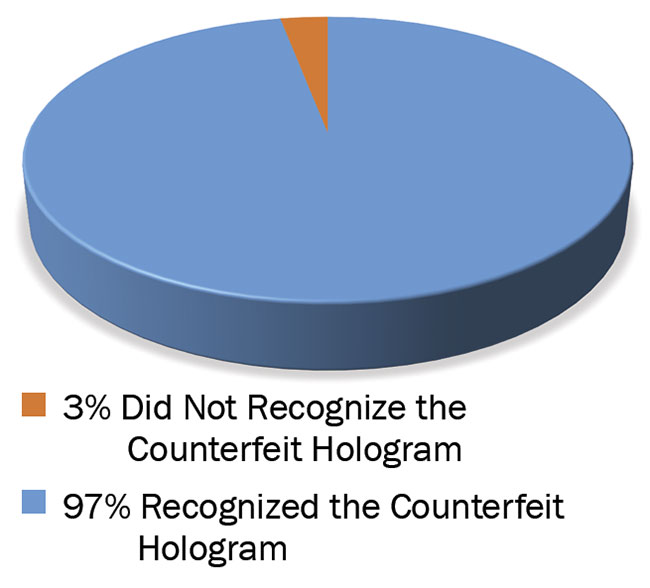
Figure 3. The vast majority of people surveyed recognized the counterfeit hologram without prior education. Courtesy of 3D AG.
Can an educated consumer identify the real hologram by authenticating overt holography effects?
The survey participants were educated to look for specific features. The features
were explained and then the four holograms were shown. Participants were asked to find the hologram with the real object recording (the object was shown), and a special 3D effect was explained as “movement of the round graphical elements in the plane.” This minimal education in the form of a precise description of effects resulted in a playful movement of the holograms during inspection by the surveyed: 86% inspected the special 3D effect, while 84% inspected the real object recording. It could therefore be determined that a consumer could be educated to identify effects and the real hologram, especially effects originated
by analog classical holography (Figure 4).
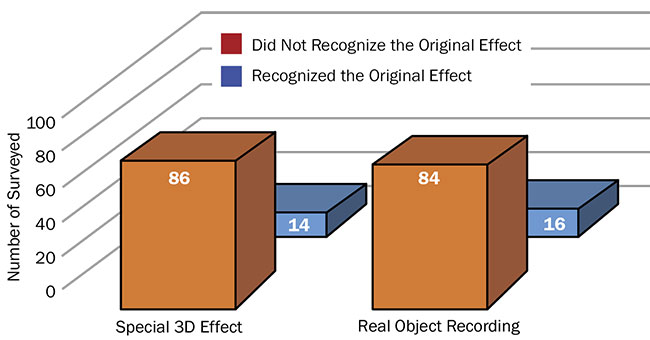
Figure 4. Rates of identification of specific effects for authentication, with prior education. Courtesy of 3D AG.
This comparison of the original, similar holograms with a counterfeit hologram helped prove the hologram’s potential. The survey obtained valuable data on
the perception of holograms, and the
findings support that holography is a viable solution for product and brand protection.
Not only is the counterfeiting industry growing rapidly each year, the number of anti-counterfeiting features are simultaneously expanding. Furthermore, the authentication power of holograms has needed justification due to the rise of digital origination technologies. With the first hypothesis, it is understood that holography is generally trusted. Holograms have also proven to be the most widely known anti-counterfeiting approach, and their presence clearly gains attention. The educated and uneducated inspection tests support the second and third hypotheses. The knowledge acquired by conducting the test with educated consumers proves that holography is a viable solution, as it allows educated consumers to authenticate holograms.
The success of the technology comes back to communication — the most important factor. With today’s multiple options for communicating with consumers over various channels, it is possible to educate in a simple manner. It has also been proven that consumers can be easily educated to properly view a hologram via simple instruction and the light of a mobile phone. If brand owners are looking to implement holography, this study about different technologies shows that a hologram may not always be trusted and that companies need to inform themselves about the origination technology and the security levels applied in the brand protection solution. If properly applied, a hologram still represents a solid anti-counterfeiting feature and a viable solution for product and brand protection.
Meet the authors
Martina Müller is CEO of 3D AG. She has a background in art and chemistry and a degree in business administration from HWZ Zürich. Müller focuses on spreading the use of holography for anti-counterfeiting purposes.
Marek Krehel, Ph.D., is director of technologies and R&D at 3D AG. He received his doctorate from ETH Zürich for his work on optical fibers for biomedical sensing. Krehel now develops functional and holographic structures on a large scale.
References
1. W.E. Kock (1981). Lasers and Holography. 2nd ed. Toronto: General Publishing
Company, p. ii.
2. B. Kluepfel and F. Ross (1991). Holography Marketplace. 3rd ed. Berkeley, Calif.:
Ross Books.
3. P. Hariharan (1996). Optical Holography: Principles, Techniques, and Applications. 2nd ed. Edinburgh: Cambridge University Press.
4. R.L. van Renesse (May 2004). Security
aspects of commercially available dot
matrix and image matrix origination systems. Proc SPIE, SPIE International Conference on Optical Holography and its Applications, Kiev, Ukraine.
5. J. Drischel (2004). A New Framework for Combating Piracy and Counterfeiting.
Bristol, England: GRIN Verlag.
6. 3D AG study. Full study can be requested at: [email protected].